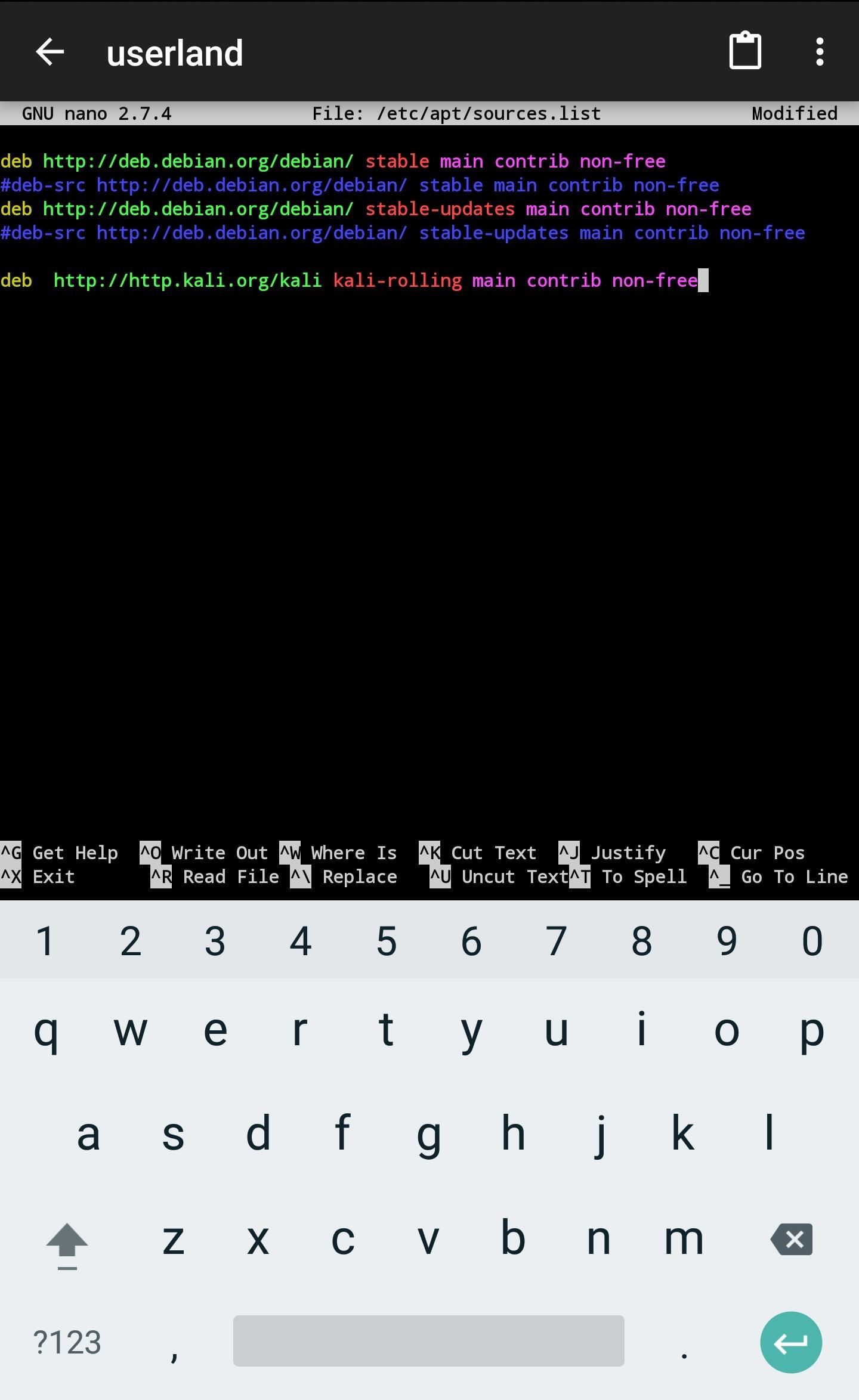
Male hacker uses the mobile phone to hack the system. Concept of cyber crime and hacking electronic devices Stock Photo | Adobe Stock

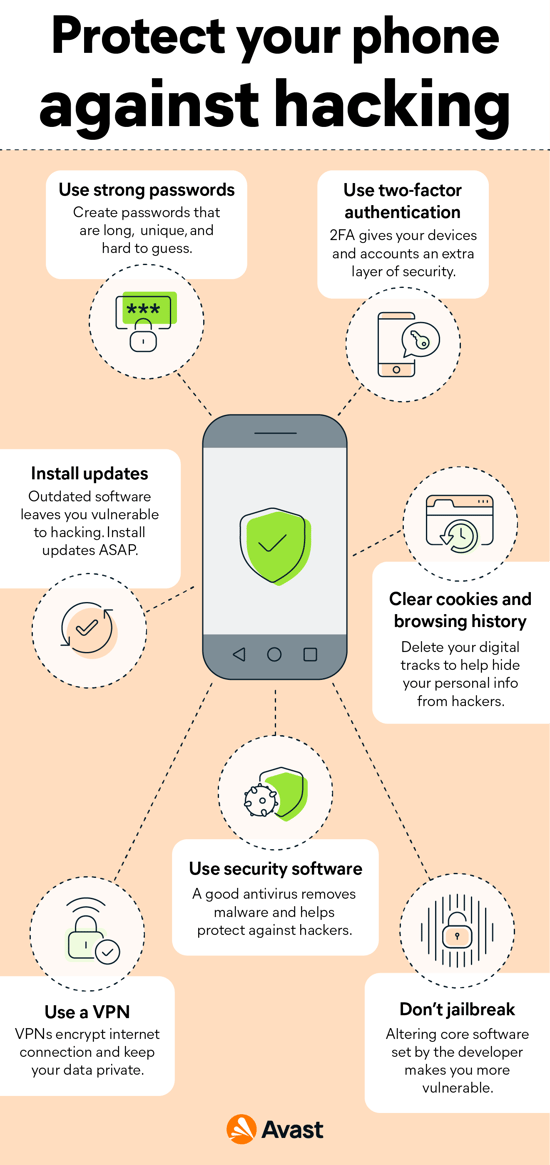
Explained: How Pegasus works to infiltrate your phone with a 'zero-click' option - Hacker-for-hire | The Economic Times